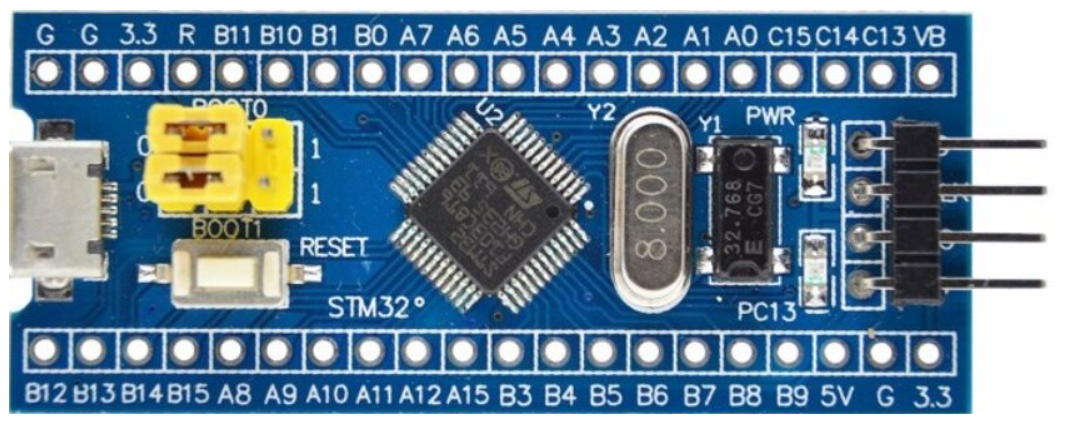
Chapter 10 Vendor: STM32 Embedded Systems Security and TrustZone
A free ebook on Embedded systems security, TrustZone, and reverse engineering firmware.
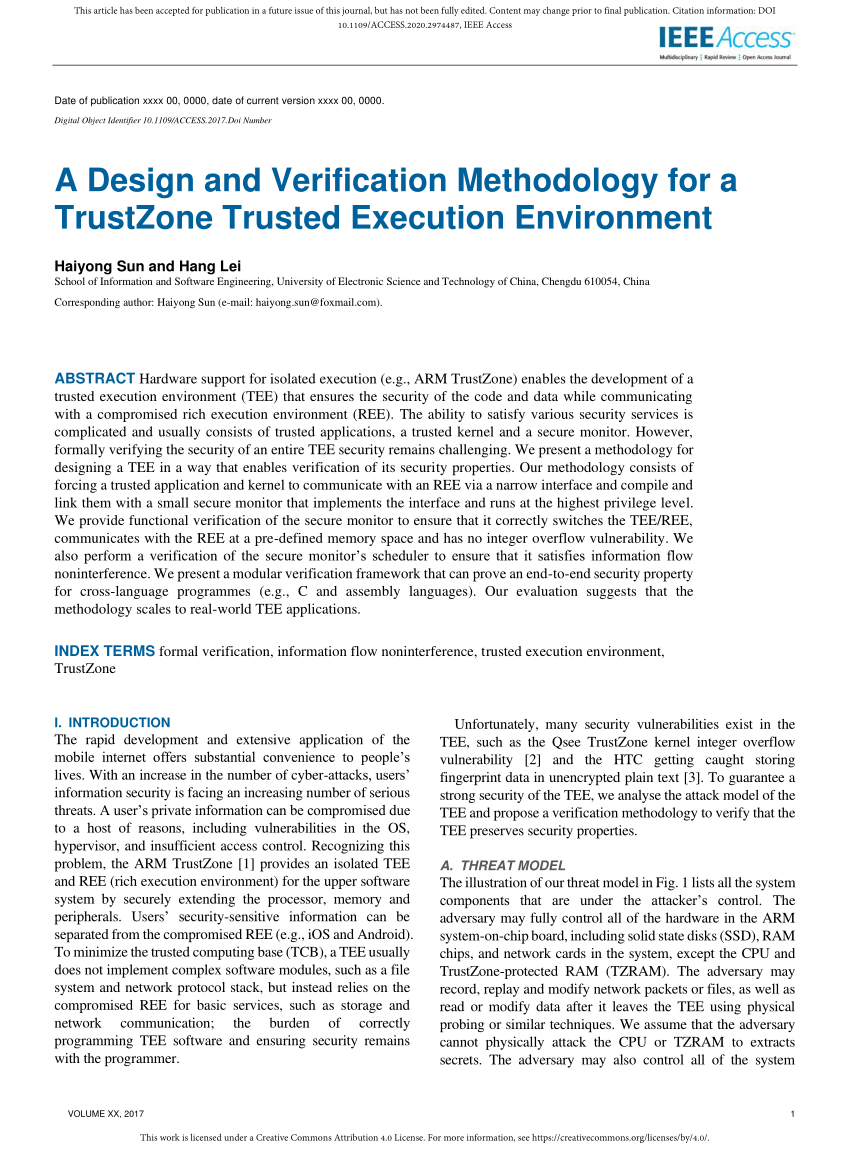
PDF) A Design and Verification Methodology for a TrustZone Trusted Execution Environment

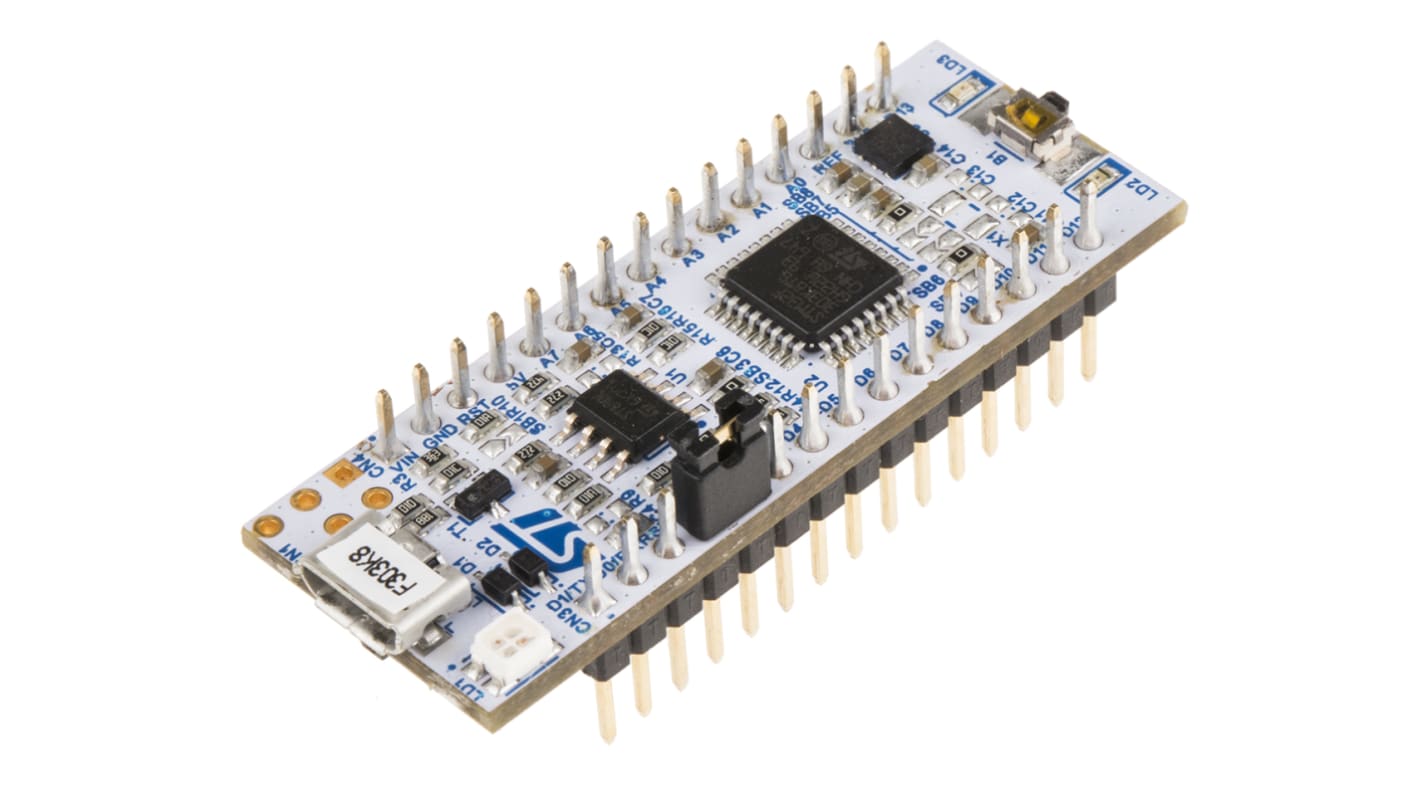
Chapter 4 Basics: TrustZone-M Embedded Systems Security and TrustZone
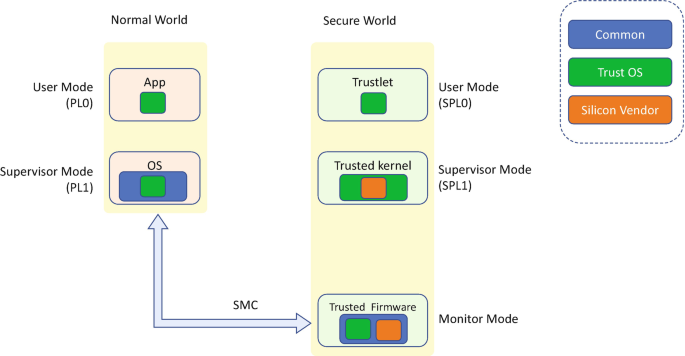
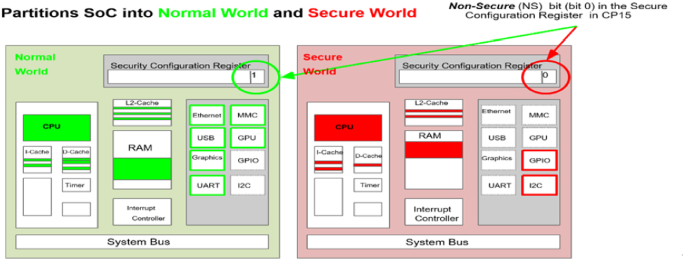
Trusted Execution Environment

Using TrustZone for Armv8-M

20 Best Embedded Systems Books of All Time - BookAuthority
Attacking TrustZone on devices lacking memory protection
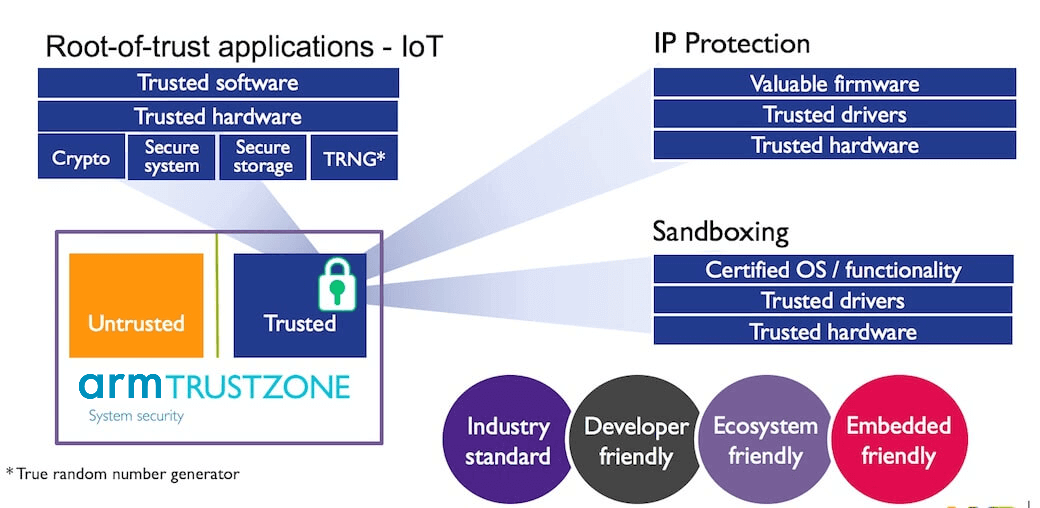
Designing secure embedded IoT devices - Architectures and Processors blog - Arm Community blogs - Arm Community

Package boosts security of STM32 code
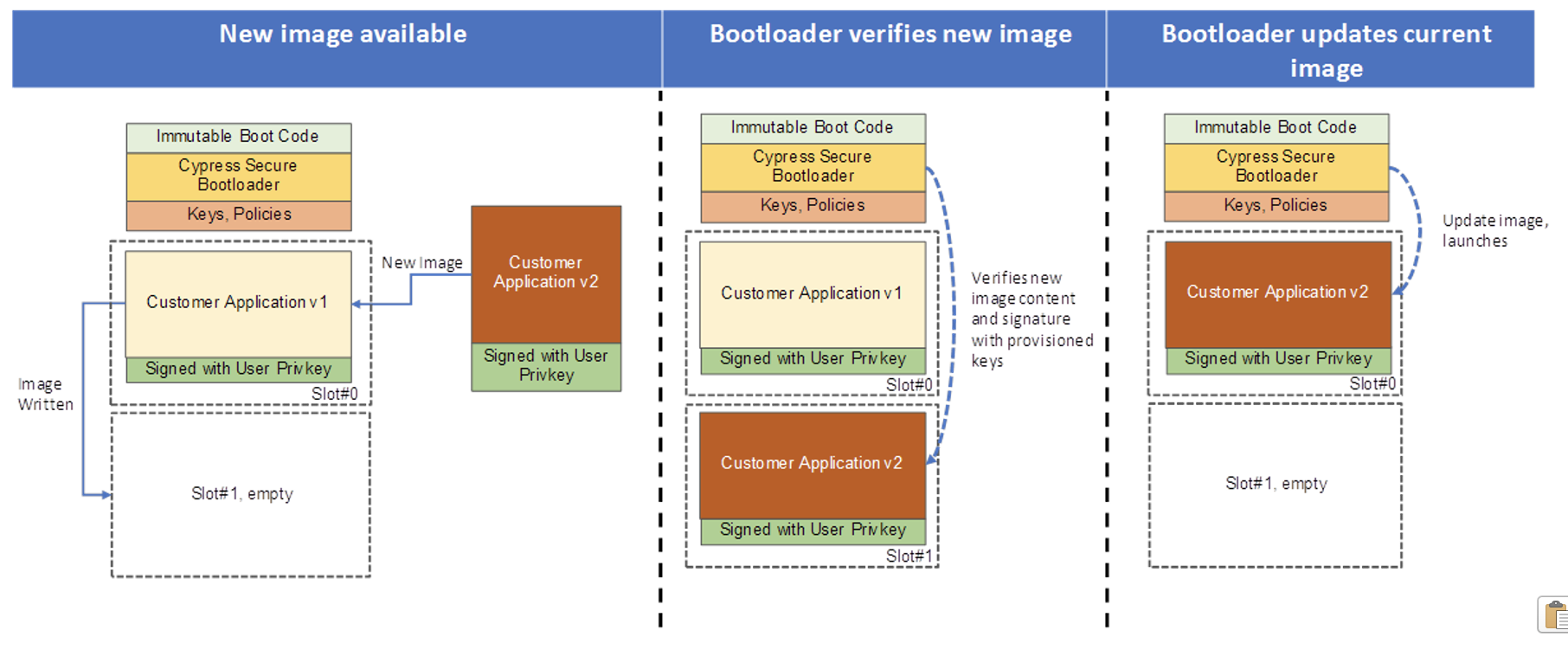
5 Elements to Secure Embedded Systems – Part #4 Secure Bootloaders
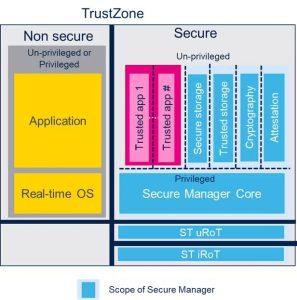
STM32Trust TEE: in-depth explanations of and discussions on Secure Manager, our turnkey security solution for STM32 at the system level
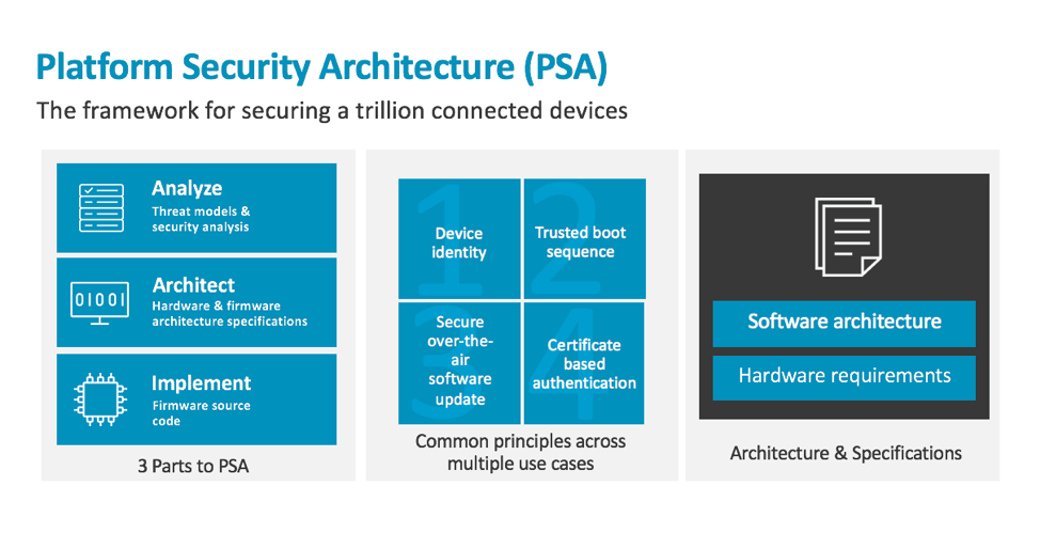
Embedded security with TrustZone-enabled microcontrollers - Architectures and Processors blog - Arm Community blogs - Arm Community

Chapter 1 Introduction Embedded Systems Security and TrustZone

Attacking TrustZone on devices lacking memory protection